How can we help you today?
SharePoint File Share Access Setup Guide
MyWorkDrive 6.4 Server or higher Required:
SharePoint is a web-based collaboration and document management platform by Microsoft which can be integrated with MyWorkDrive for file access and storage services. SharePoint File Share Access allows MyWorkDrive Servers to connect to SharePoint Sites, Libraries and Folders and make them available to users via the MyWorkDrive Web Browser, Desktop and Mobile Clients.
Contents
The default option utilizes our MyWorkDrive Cloudflare Integration and our shared MyWorkDrive Azure AD App Registration. With the default option the customer does not need to create their own Azure AD App Registration or create a Public Web Address to the internal MyWorkDrive Server. To enable SharePoint Access simply enable our default option in Integrations, Storage Providers – SharePoint.
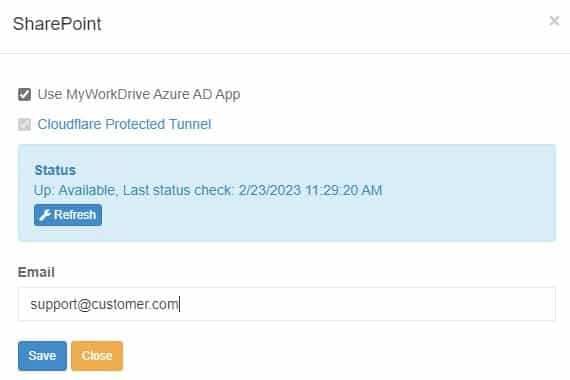
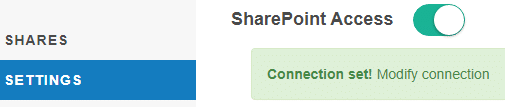
Enable SharePoint Access in Settings: SharePoint Access
With SharePoint Access configured in integrations and enabled in settings, create a share using SharePoint as the Storage Type and select the users or groups who are assigned access in MyWorkDrive::
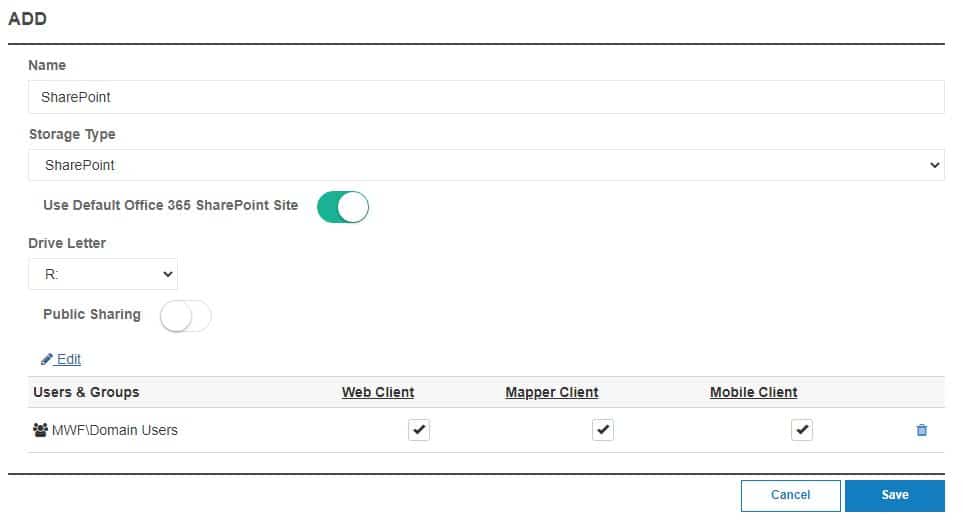
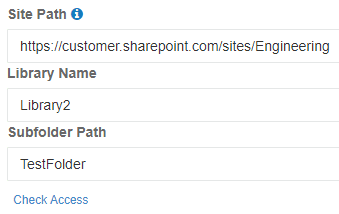
The Default Option will create a share and use the company’s default SharePoint Site in Microsoft Office 365. Optionally, select and add a custom site using the URL of the site and optionally specify a Library and/or Subfolder. Click Check Access to validate the site.
Allowed Tenant ID
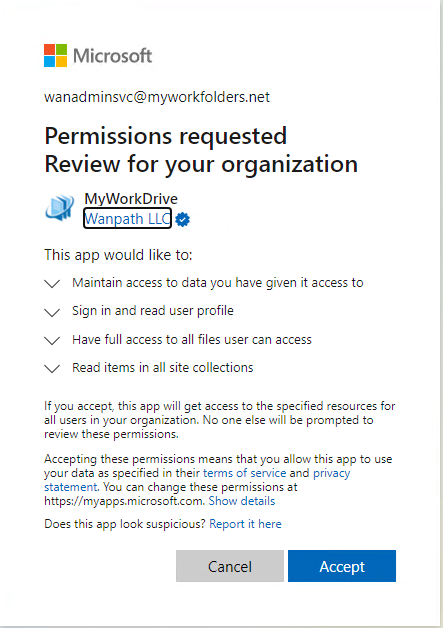
We recommend all customers approve and restrict which allowed Azure AD Tenant ID’s are enabled for SharePoint Access. The Allowed Tenant ID option provides 2 capabilities:
- Approval of the Azure AD Application for use by all users in the organization
- Restricting login to the Application to only users with accounts in the internal organization (custom app registrations only).
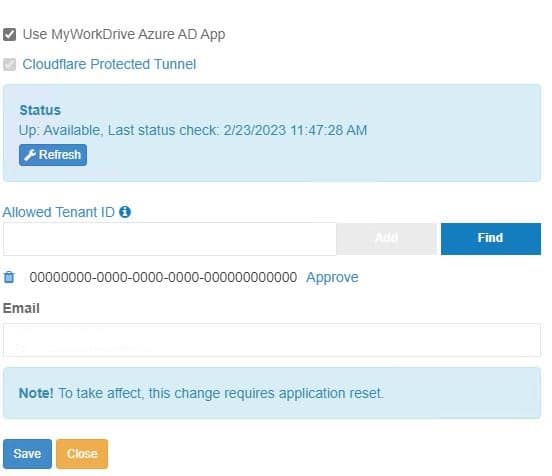
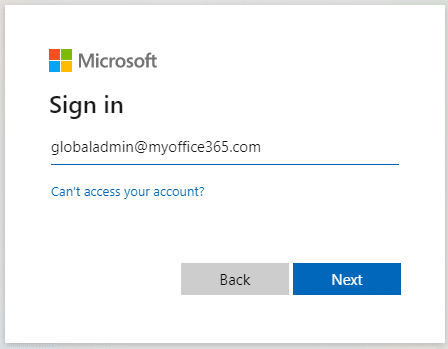
After Entering the Tenant ID click Approve. Login with a global administrator with rights on your Azure AD to approve applications for your organization:
Accept and grant Permissions for your organization:
The link in the first paragraph shows you how to find your tenant, you may also be able to use a site like https://www.whatismytenantid.com/ to obtain your tenant ID.
Setup Custom Azure AD App Registration
As an alternative to our our shared MyWorkDrive Azure AD App Registration, MyWorkDrive supports creating a customer Azure AD App.
Each organization will need their Azure AD Global Admin to create an Azure AD App registration.
Create a new Azure AD App Registration in the same Azure AD as your user’s Office 365 Subscription where your SharePoint Site(s) are hosted. This will be used to allow the MyWorkDrive server to connect to SharePoint Sites.
On portal.azure.com, login using Global Admin Account. Bring up Azure Active Directory: https://portal.azure.com/#blade/Microsoft_AAD_IAM/ActiveDirectoryMenuBlade
Click App Registrations: Create New Registration
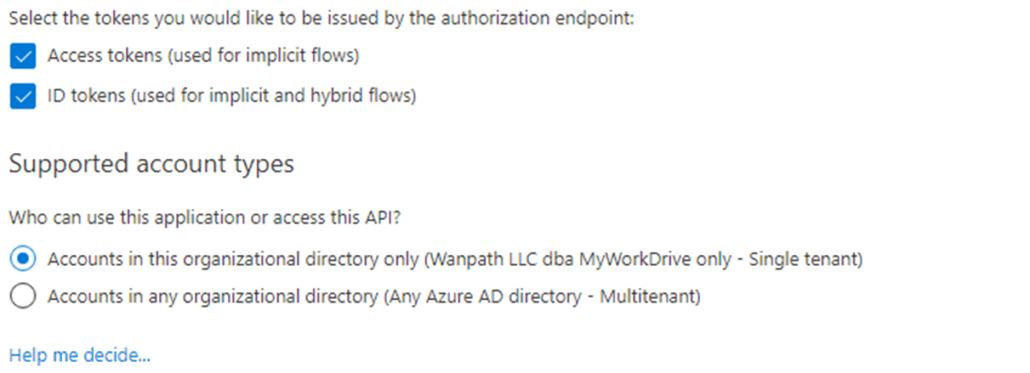
Provide a Name, Selected Account Types and insert your public MyWorkDrive URL with subsite added of /GraphApiTokenPage.aspx
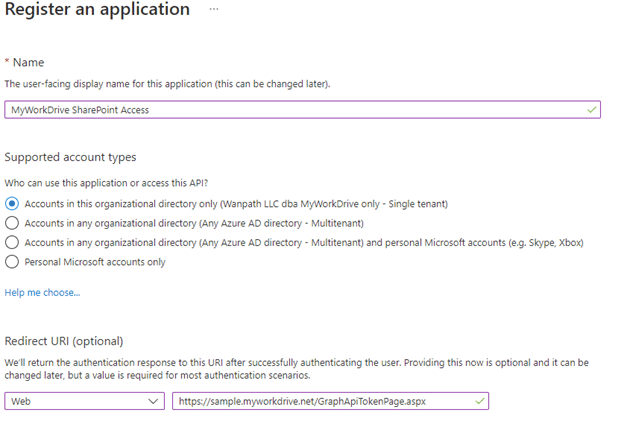
Click Register
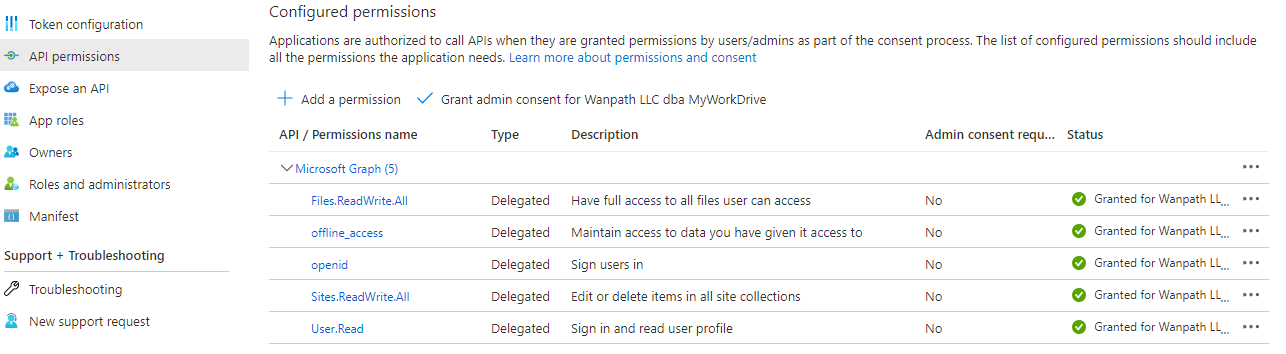
API Permissions
Click API permissions, Add Graph API Delegated Permissions: Microsoft Graph – Files.ReadWrite.All, offline_access, openid,Sites.ReadWrite.All, User.Read
Click to Grant admin Consent for your company.
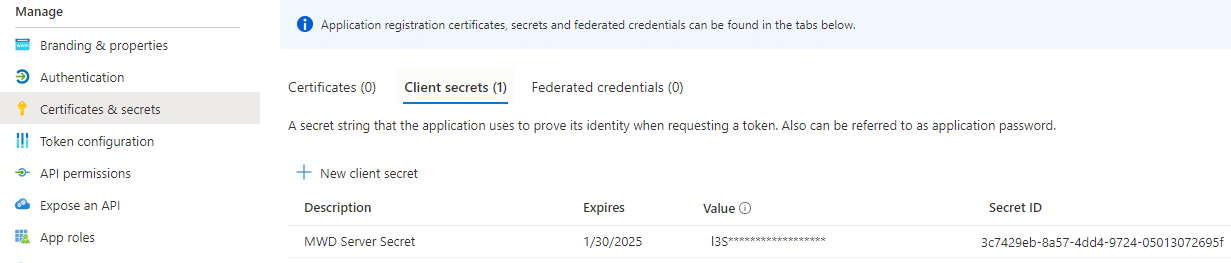
Create Client Secret
Click Certificates & Secrets: New client secret
Note and Calendar Secret Expiration Date as it will need to be regenerated at that time and updated on all MyWorkDrive Servers.
Copy the Client Secret Value (not the secret ID): Keep this backed up and secured as it will only display briefly.
Click Overview: Copy the Application (client) ID: Retain this value for use in the MyWorkDrive Admin Panel.
Copy the Directory (tenant) ID: Retain this value for use in the MyWorkDrive Admin Panel.
*Note the Client Secret Expiration – this will need to be renewed before it expires and updated on each MyWorkDrive Server in the future.
Authentication
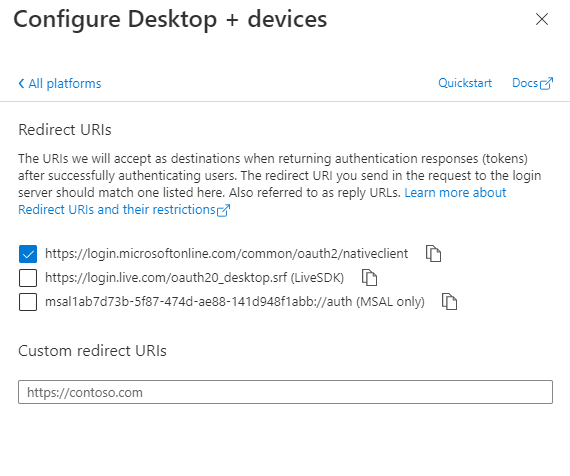
Click Authentication, Click Add Platform, Choose Configure Desktop + Devices, Check the native client option:
Enable Access Tokens and ID tokens
MyWorkDrive Server Configuration
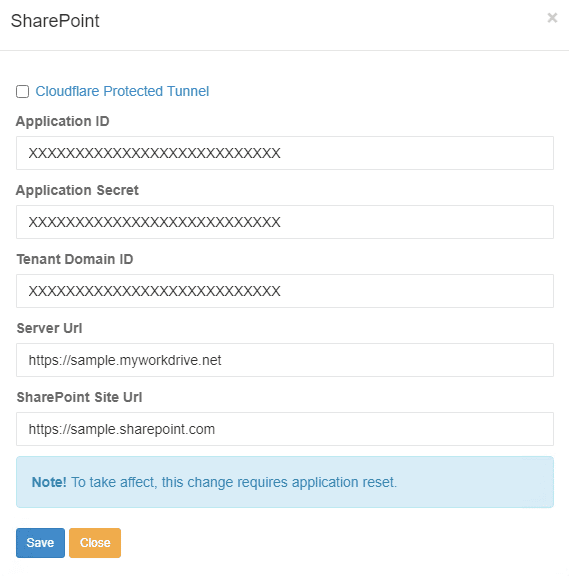
Paste the values of the Azure AD Application ID, Secret, Single Tenant Domain ID, Your Server URL and finally your SharePoint Site URL: