How can we help you today?
OneDrive Office Online Editing Server Setup Guide
Contents
OneDrive Office Editing Overview
The OneDrive Office Online editing option allows users with OneDrive business accounts in the organization to edit files in Office Online that automatically save changes back to MyWorkDrive file shares.
The Office Online editing works by caching the file to the users OneDrive Work account, placing a lock on the file through MyWorkDrive to the Windows File Share, monitoring the file for edits and coedits and finally removing it once editing is completed.
The default option utilizes our MyWorkDrive Cloudflare Integration and utilizes our shared MyWorkDrive Azure AD App Registration. With the default option customer does not need to create their own Azure AD App Registration or create a Public Web Address to the internal MyWorkDrive Server.
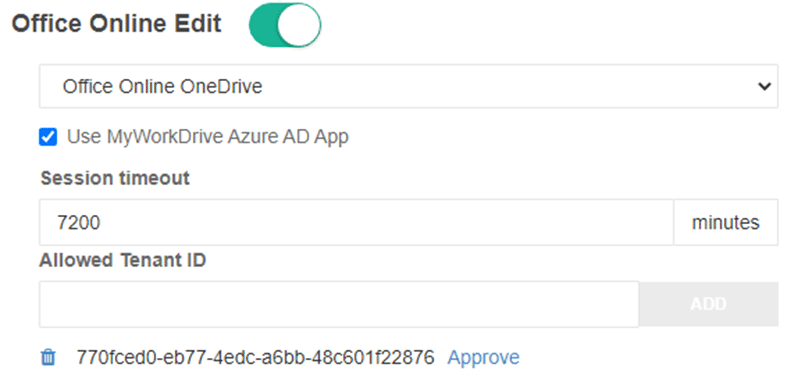
Allowed Tenant ID
We recommend all customers approve and restrict which allowed Azure AD Tenant ID’s are enabled for Office Online Editing. The Allowed Tenant ID option provides 2 capabilities:
- Approval of the Azure AD Application for use by all users in the organization
- Restricting login to the Application to only users with OneDrive accounts in the internal organization.
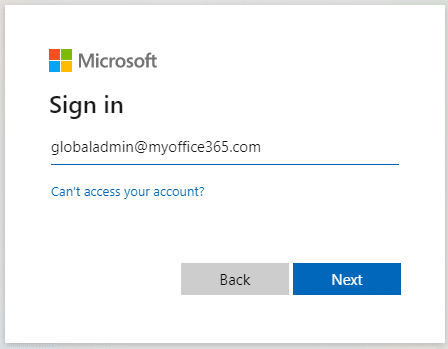
After Entering the Tenant ID click Approve. Login with a global administrator with rights on your Azure AD to approve applications for your organization:
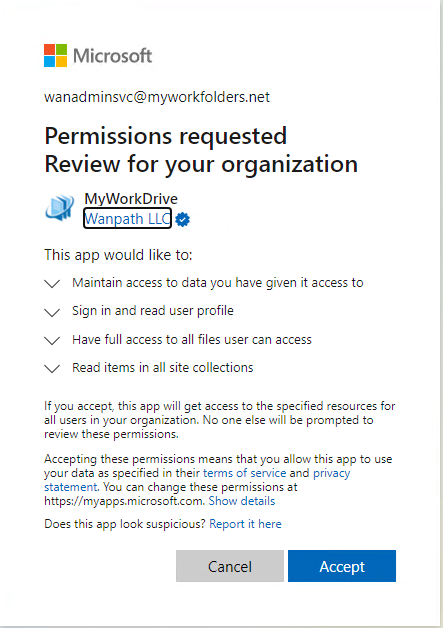
Accept and grant Permissions for your organization:
The link in the first paragraph shows you how to find your tenant, you may also be able to use a site like https://www.whatismytenantid.com/ to obtain your tenant ID.
Session Timeout
Customers may alter the default Session timeout as desired.
Custom Azure AD App Registration
Optionally each organization may create their own Azure AD App registration that will allow the Microsoft Graph API Access as an internally published app and use their own direct server URL.
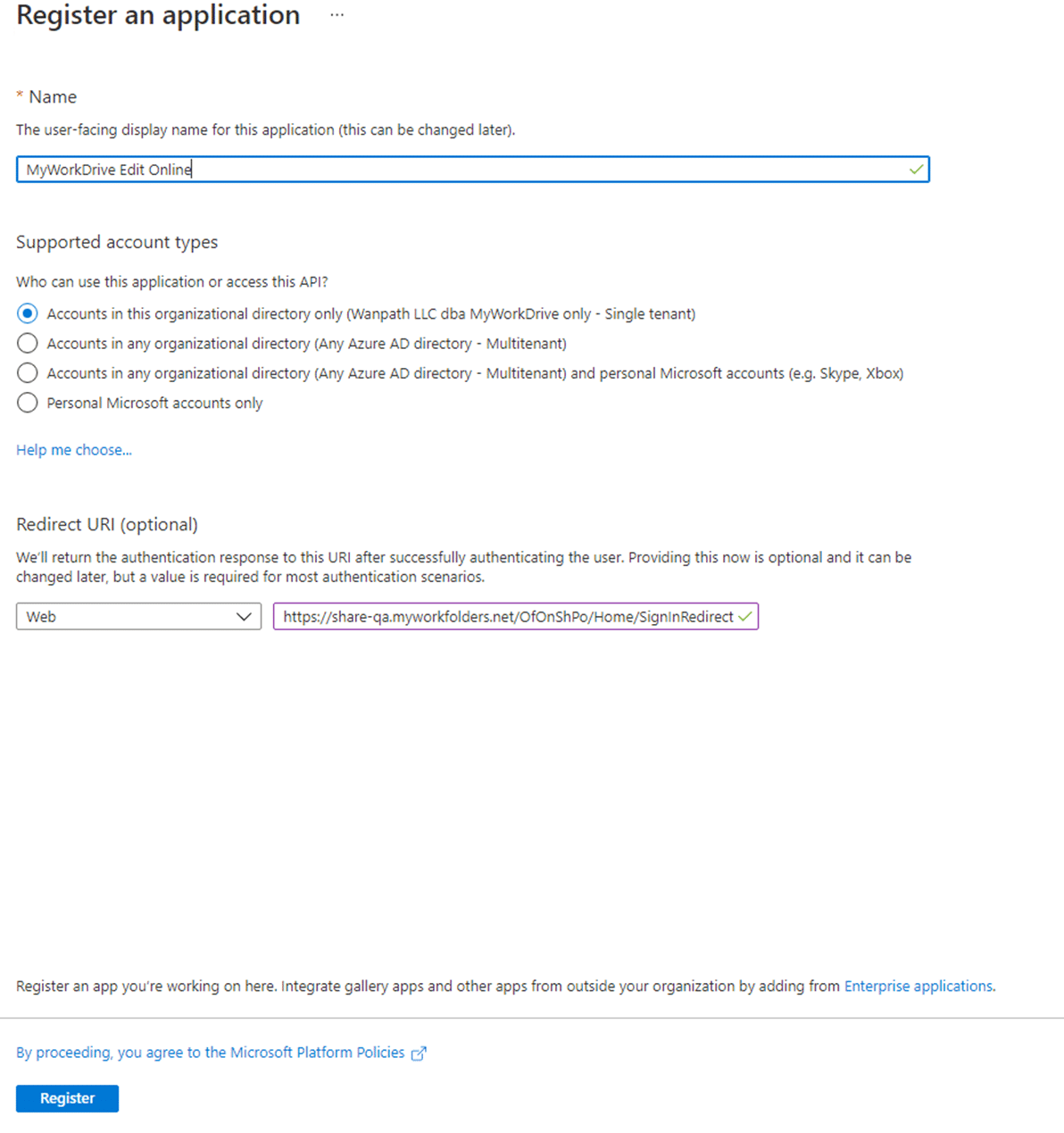
Create a new Azure AD App Registration in the same Azure AD as your user’s Office 365 Subscription. This will be used to provide delegated graph API access.
On portal.azure.com, login using Global Admin Account. Bring up Azure Active Directory: https://portal.azure.com/#blade/Microsoft_AAD_IAM/ActiveDirectoryMenuBlade
Click App Registrations: Create New Registration.
Provide a Name, Selected Account Types and insert your public MyWorkDrive URL with subsite added of /OfOnShPo/Home/SignInRedirect for example: https://share.mycompany.com/OfOnShPo/Home/SignInRedirect
Click Register:
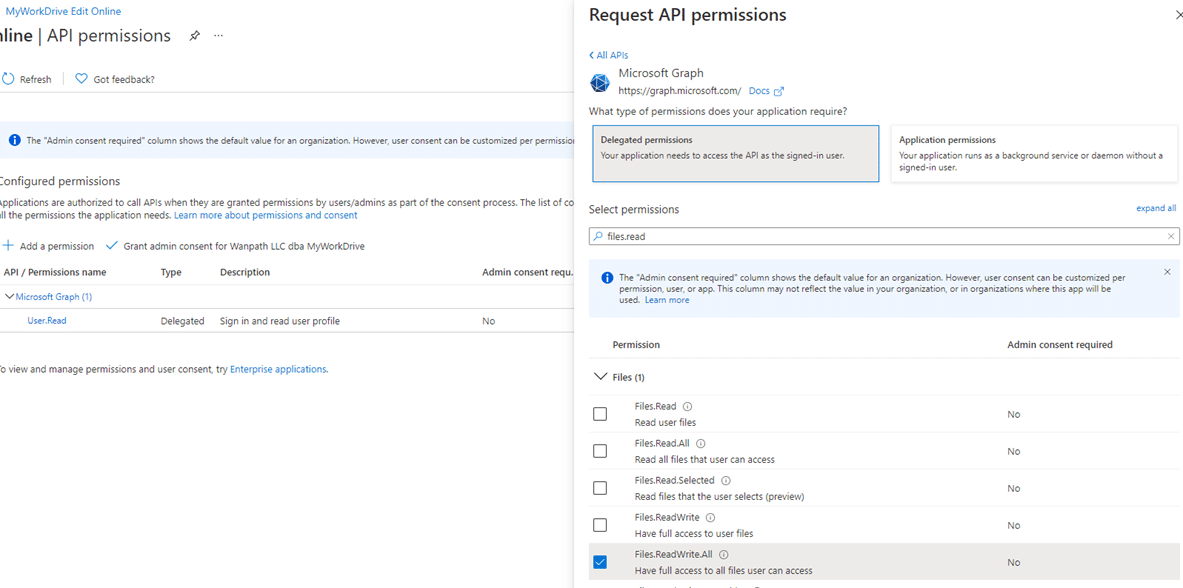
Click API permissions, Add Graph API Delegated Permissions: User.Read Files.ReadWrite.All Sites.Read.All
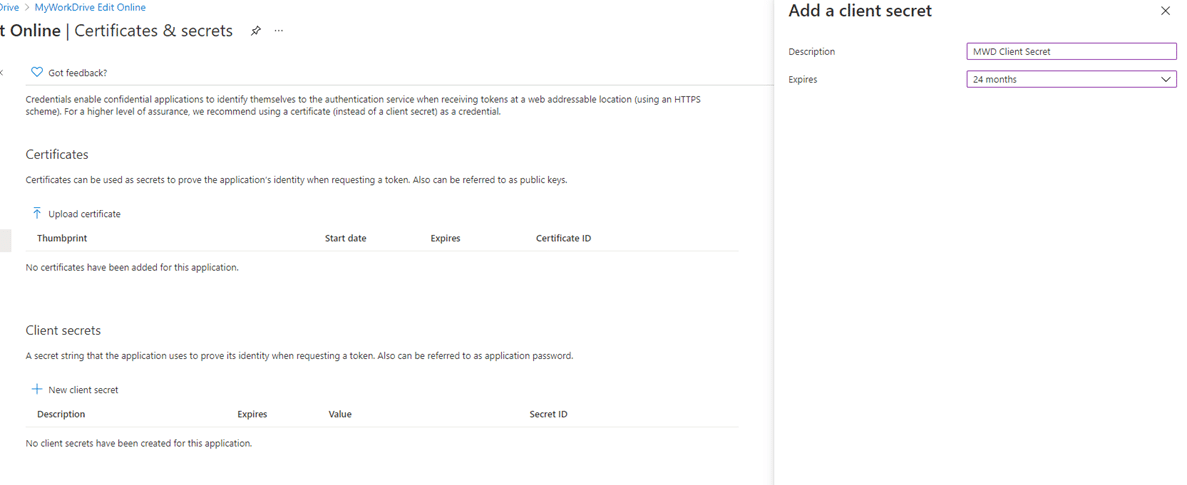
Create Client Secret: Certificates & Secrets: New client secret
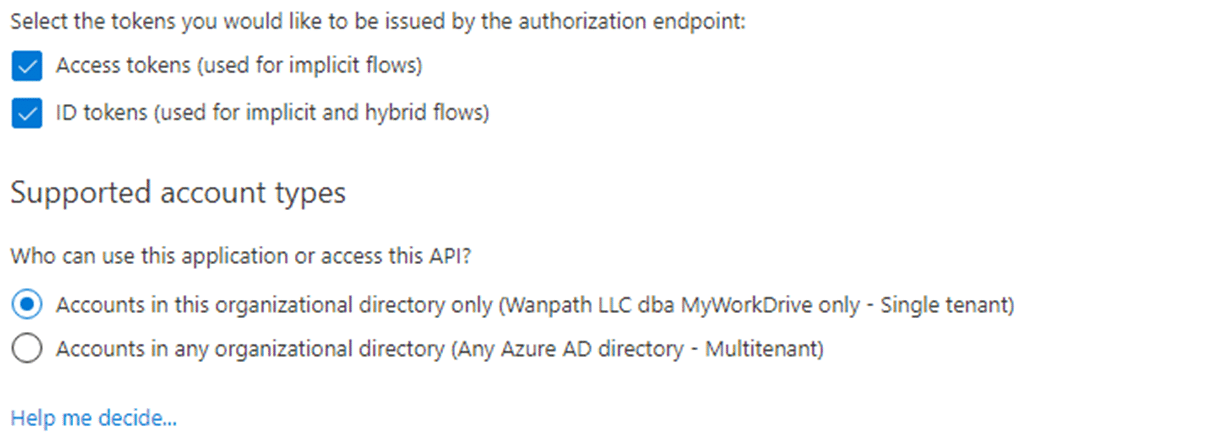
Click Authentication: Enable Access Tokens and ID tokens.
Copy the Client Secret Value (not the secret ID): Keep this backed up and secured as it will only display briefly.
Click Overview: Copy the Application (client) ID: Retain this value for use in the MyWorkDrive Admin Panel.
*Note the Client Secret Expiration – this will need to be renewed before it expires and updated on each MyWorkDrive Server in the future.
Update Branding on your custom Azure AD App Registration to verify app or add Company Logo as desired.
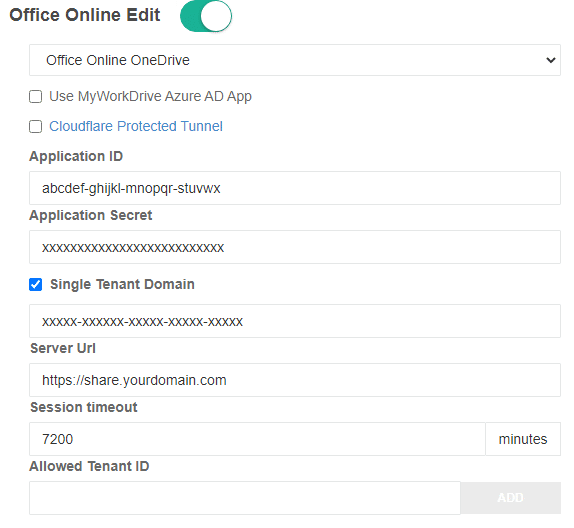
MyWorkDrive Server Custom App Configuration
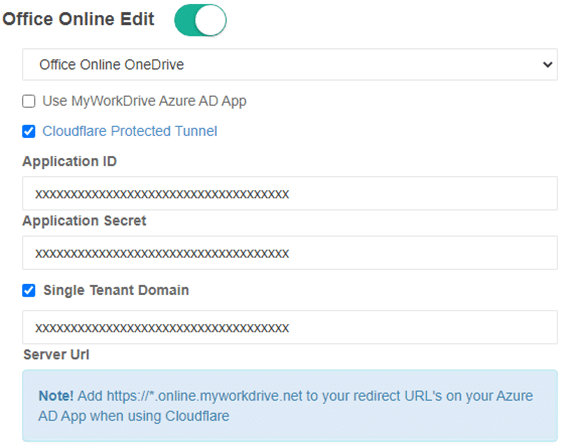
Paste the values of the Azure AD Application ID, Secret, Your Server URL and Optionally your Azure Tenant ID (if your Azure AD Application is set to only Accounts in this organizational directory – Single tenant) into the settings section under Office Online OneDrive Edit option.
Optional:
Instead of using your own Public Server URL you may use our Cloudflare assigned hostname under our MyWorkDrive.net domain. Cloudflare Tunnel requires TCP port 7844 outbound from your server to Cloudflare IP’s. When Cloudflare is used, you will need to enter https://*.online.myworkdrive.net as an allowed host to your Custom Azure AD Application instead of using your own host name values.
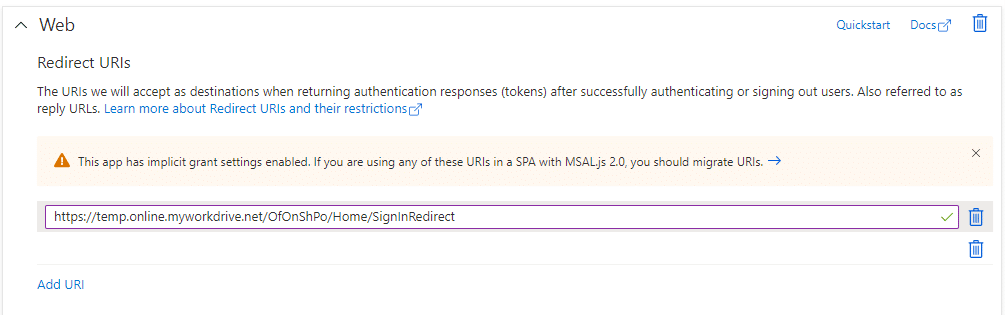
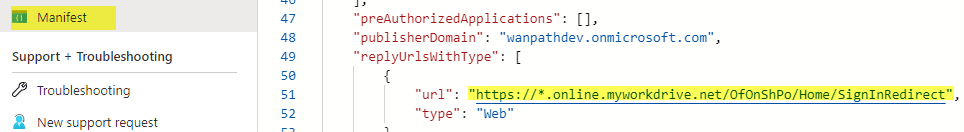
Azure AD App Registrations do not allow entering in a wildcard directly. To enter in a wildcard, insert a temporary address such as https://temp.online.myworkdrive.net/OfOnShPo/Home/SignInRedirect.
To update the URL click Manifest to edit the Manifest and update the temporary URL to https://*.online.myworkdrive.net/OfOnShPo/Home/SignInRedirect.
Office Online Editing using OneDrive site should now be ready for testing using your Custom Azure AD App Registration.
File Locking & Monitoring Process
When files are opened using the OneDrive Editing option, they are locked on the MyWorkDrive Server and set to allow co-editing. If other users wish, they may co-edit the file in Office Online through the browser. Traditional Mapped Drive or Local office users will receive a file locked message while the user has the file open for edit in Office Online OneDrive Edit.
MyWorkDrive server will monitor files for changes every 1 minute. If changes are found they will be copied the Windows File Share. If no changes are found, MyWorkDrive will attempt to determine if the user has completed editing. If user closes the browser tab the file will be removed from OneDrive immediately after copying changes back to the Windows File Share through MyWorkDrive. If communication is lost MyWorkDrive will attempt to remove the file until it is unlocked on OneDrive.
MyWorkDrive will attempt to close the user’s browser tab if no changes are made to the document that exceed the overall idle timeout setting.
Additional Session Timeout Settings
To prevent users from keeping idle files open for coedit, customers may wish to set idle timeout settings https://docs.microsoft.com/en-us/sharepoint/sign-out-inactive-users.
- The policy is applicable to entire tenant and cannot be scoped to user/users or SharePoint sites.
- It will not sign out users who are on managed devices or select Keep Me Signed In during sign-in (It will not sign out users who are on managed devices or select Keep Me Signed In during sign-in).
Conditional access policies may also be used https://docs.microsoft.com/en-us/azure/active-directory/active-directory-conditional-access-technical-reference#cloud-apps-assignments.
Coediting
Coediting in Office Online is fully supported. Multiple users may edit the same document with MyWorkDrive similiar to co-editing a document sourced from SharePoint.
File locking may note the original user who opened the file as the editor, as their OneDrive is the location the file is stored, but the other user’s editing sessions are valid.
Coediting is not supported across Microsoft Tenants. All users Office Licenses must be in the same tenant.