Azure Files Remote Access with MyWorkDrive
Contents
Azure Files Overview
Microsoft Azure file shares are windows file shares hosted by Azure. By utilizing Azure Files, companies are relieved of the responsibility of maintaining Windows file server-based file shares. Azure Files offers fully managed file shares in the cloud that are accessible via the industry standard SMB protocol or via HTTPS over API.
To map drives remotely to Azure file shares requires connecting to ports 445 over SMB protocol, which may be blocked by internet providers and only accessible from the same local area network or via VPN. Businesses will need to maintain VPN tunnels from Azure to each location as well as VPN gateways for users to access files on the go.
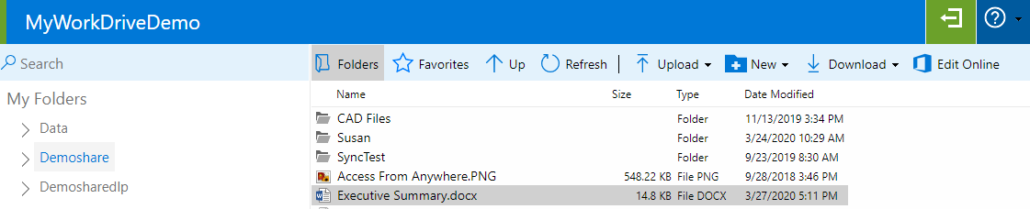
- Connect through a Web Based File Manager with your Azure AD/Entra credentials from any device (PC’s do not need to joined to the domain).
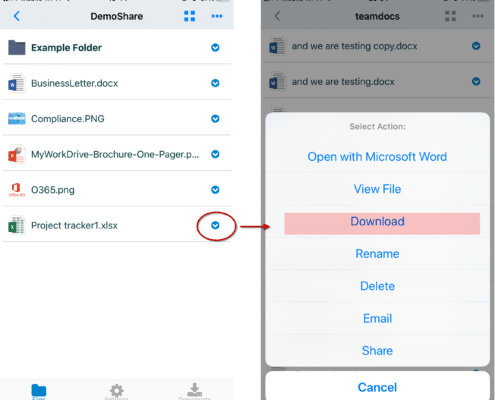
- Connect using iPhone or Android Apps.
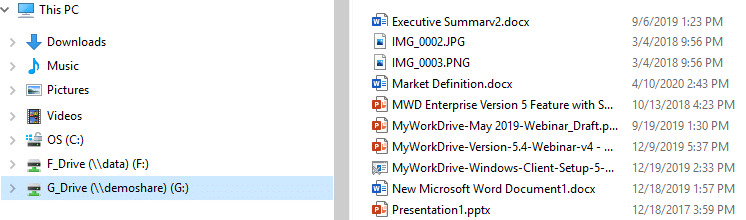
- Use the MyWorkDrive mapped drive client that works over HTTPS (no VPN needed).
Use Azure Files with MyWorkDrive to get the elasticity and ease of management of cloud storage.
- Durable and highly available cloud storage fully managed by Microsoft.
- Pay as you go storage. Only pay for what you use. Up to 100TB per share.
- Connect to Azure File Shares using https instead of port 445 without VPN.
- File are encrypted in transit and at rest.
- Secure access with two factor authentication (2FA) & conditional access policies.
- Use Azure AD Entra Authentication to eliminate maintaining Active Directory Domain Controllers.
- Azure File Sync
- Bi-directional sync between on-premise and Azure file shares.
- Local caching and cloud tiering. Performance of on-premise storage with scale and elasticity of the cloud.
- Multi-site sync to have a cache at each branch office with centralized cloud storage.
The combination of MyWorkDrive and Azure Files is a great match!
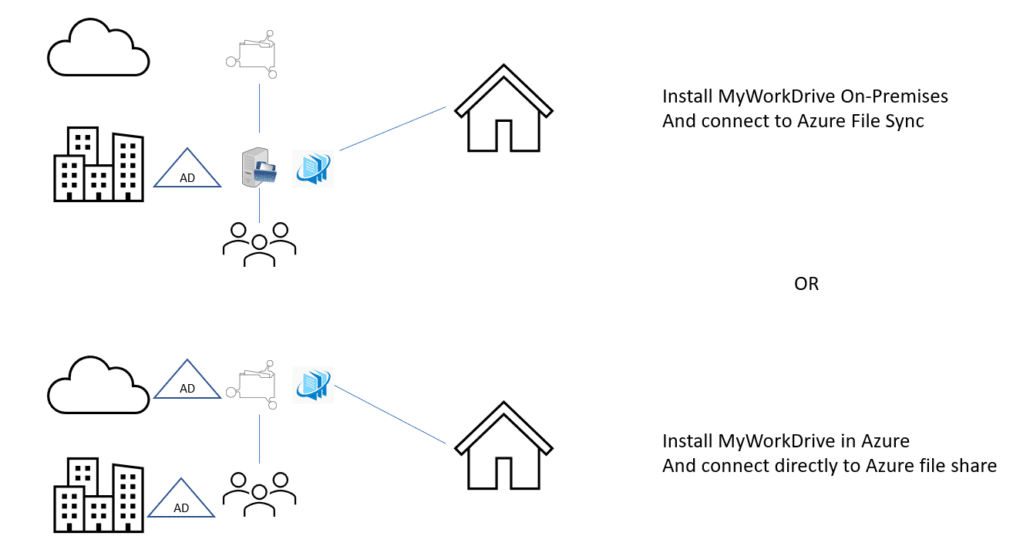
Option 1: Directly Connect Azure Files with MyWorkDrive
MyWorkDrive supports connecting to Azure file shares using Azure AD (Entra) id authentication over API or by using Active Directory domain joined Azure file shares over SMB. In our support article here, we present our authentication options for connecting MyWorkDrive to Azure file shares directly with MyWorkDrive hosted in Azure using Azure AD (Entra) authentication over API or by using Active Directory Authentication with SMB.
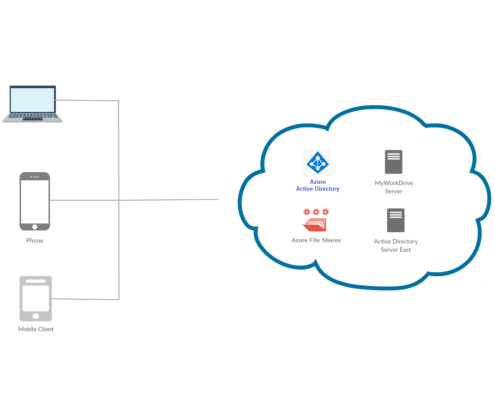
Option 2: Connect Azure File Sync with MyWorkDrive On-Premise
With Azure Files Sync multiple locations can be sync’d from on-premise to Azure Files and remote locations. Using Azure File Sync is another alternative to connect your Active Directory, since NTFS ACL’s are synced, in addition to files and folders. Furthermore, Azure File Sync supports preserving, inheriting, and enforcing Microsoft file system NTFS ACLs on all folders and files in a file share.
To connect MyWorkDrive to Azure file shares, simply point them to the local server hosting the sync copy of your Azure file shares. From a MyWorkDrive perspective, nothing has changed – NTFS permissions and file locks are honored.
Azure File Sync extends file services from on-premise to Cloud Storage on Azure file shares and across Windows Servers in multiple locations. Microsoft engineers interviewed customers and confirmed that Windows File Shares are still in use for a multitude of reasons. The customer pain points identified include speed of access, control of data and large storage capacities. Azure File Sync addresses these concerns.
Azure File Sync Key Features
- Bi-Directional Sync – from Windows Server to Azure Cloud Storage with write back capabilities
- Multi-Site Sync – Sync a share across multiple Windows Servers through Azure file shares to Cloud Storage with the ability to cache and edit data in real time at each site.
- Backup of Azure file shares to Azure Backup
- Tiering of data – set the maximum data storage capacities for each Windows Server and only replicate the most recent data to each server with the balance stored in Azure file Shares in the cloud.
Using MyWorkDrive, Windows file shares can be accessed from any location worldwide over HTTPS (port 443) from any Web Browser, the MyWorkDrive mapped drive client or mobile clients.
