Overview
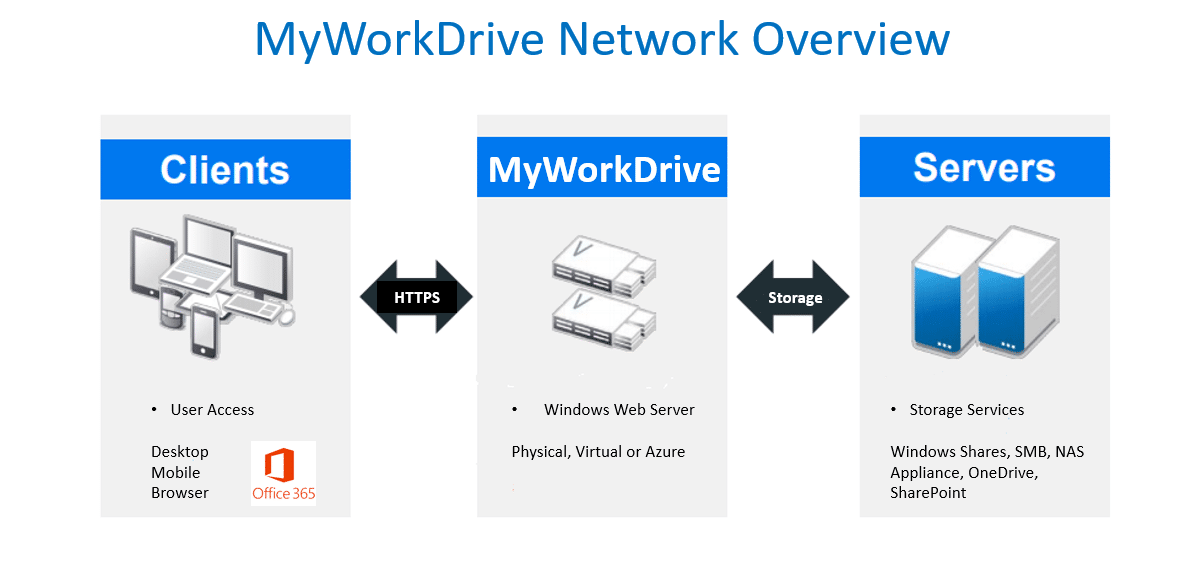
Administrators may wish to lock down the MyWorkDrive Server client site to be accessible from only restricted networks or not publish the site and allow access from internal LAN segments only. This would typically be used where the administrator wishes to provide access to the Web File Manager site for view and editing documents in Office 365 but restrict external access. View typical network deployment scenario diagrams here.
Firewall lockdown is possible and MyWorkDrive will function and allow Office online document editing even if restricted to company WAN IP’s or LAN segments only with the following caveats:
- OneDrive external file sharing will not function (a publicly accessible Web File Manager URL is needed for Microsoft to copy files to OneDrive) unless the server can access https://*.live.com and https://wp-onedrive-api.wanpath.net for OneDrive external sharing.
- An internal host name must be used to reference the site for internal file sharing – for example: https://share.mycompany.local if referenced on the internal LAN only.
- Office 365 Editing must be enabled on the MyWorkDrive Server Admin Panel.
Please note Office online editing will function even if the Web File Manager client site is locked down since it is made available during Office online editing transactions on a session basis through our MyWorkDrive reverse proxy in Azure locked down to Microsoft Office online hosts only. Full details are in this article. In additional to firewall lockdown we also recommend disabling unneeded ciphers. See our Steps to lock down IIS SSL for Compliance and Security for additional information.
Outgoing firewall requirements
To function correctly the MyWorkDrive Server needs outgoing access to the following hosts and TCP ports:
- MyWorkDrive license servers at licensing.wanpath.net (7.0.1 and earlier) and licensing.myworkdrive.net (7.1.1 and later) on SSL port 443
- Port 443 to *.live.com for OneDrive external sharing along with Office 365 URL's and IP address ranges per Microsoft article here.
- Port 443 to login.microsoftonline.com for OIDC connections, when using Entra ID or Saml SSO with Active Directory, per Microsoft's article, here
Cloud Web Connector and Cloudflare Tunnels
For customers using Cloudflare Tunnels (formerly Argo Relays) with any of the following options
- Publishing your website to the internet with Cloud Web Connector (x.myworkdrive.net)
- Office Online Editing using MyWorkDrive hosted apps for Graph API connnections
- OneDrive or SharePoint Storage using MyWorkDrive hosted apps for GraphAPI connections
- Entra ID Identity with MyWorkDrive hosted app for graph API Connections
- or connections to Azure Storage using MyWorkDrive hosted apps (Graph API connections)
Those connections are relayed through Cloudflare Tunnels. Cloudflare requires TCP port 7844 outbound from your server to Cloudflare IP’s. MyWorkDrive recommends a direct internet connection - outgoing proxy services (typically web filtering) may break Office 365 online editing features and MyWorkDrive.net usage.
Beginning with version 5.3 an outgoing proxy server may be specified in the MyWorkDrive Admin Panel under settings in the format of http://hostname or IP Address and optional port number. For example http://10.10.10.10 or http://10.10.10.10:8888.
Antivirus
Warning: Antivirus software installed on the server can interfere with the ability for your MyWorkDrive to communicate with Microsoft Azure for our Office 365 and Cloud Connectors if any firewall features are enabled. Review our Antivirus article for settings and exclusions.
Troubleshooting Office 365 and Cloud Web Connector firewall issues
If basic troubleshooting of the cloud connector fails using this article begin additional troubleshooting by ensuring the Office 365 Editing feature and/or the cloud connectors are enabled on the MWD Server admin panel under settings. If enabled, check services.msc on your server for "Cloudflared Tunnel Agent". It should be running.
If the service is running and has been for at least 15 minutes, next test outbound firewall access. From a command prompt, type "Netstat -b". Note any connection for portbridge. A healthy service should show something like below with https and 7844 ports open and in and "ESTABLISHED" state.
If these are missing, check our outgoing firewall rules, remove any Antivirus software from the MWD server and ensure your MWD server has full internet connectivity. Then run netstat -b again to see if outbound connections are established.
Netstat -b healthy outbound connections Cloudflare:
[cloudflared.exe] TCP 192.168.41.111:56200 198.41.200.233:7844 ESTABLISHED [cloudflared.exe] TCP 192.168.41.111:56201 198.41.192.107:7844 ESTABLISHED [cloudflared.exe] TCP 192.168.41.111:56202 198.41.200.113:7844 ESTABLISHED [cloudflared.exe] TCP 192.168.41.111:56208 52.230.222.68:https ESTABLISHED
Test communications on port 7844 outbound to Cloudflare tunnel service.
Launch powershell on the MyWorkDrive server and type the following command:
test-netconnection -computername 198.41.192.7 -port 7844 (This IP may not be available, you can check your Cloudflare log in the MyWorkDrive logs for IP addresses the connector is attempting to use)
The results should come back like below with:
TcpTestSucceded:True: ComputerName : 198.41.192.7 RemoteAddress : 198.41.192.7 RemotePort : 7844 InterfaceAlias : Lan SourceAddress : 10.10.200.20 TcpTestSucceeded : True
If TcPTestSucceded returns false a firewall or antivirus is blocking TCP port 7844 outbound from the MyWorkDrive server and needs to be investigated.
Office Webapps Viewer
MyWorkDrive uses the Microsoft Office Webapps Viewer as the default option for viewing documents in the webclient. The Office Webapps Viewer is a hosted service from Microsoft which retrieves files from the MyWorkDrive server and renders them for the user to view, when users select to view in the Webclient. This feature requires round-trip communication with the Webapps service.
Microsoft advises the following URLs be permitted for the Office Webapps feature to function properly
• *.office.com
• *.office.net
• *.office365.com
• *.msocdn.com
• login.microsoftonline.com
• login.live.com
If access to the Office Webapps service cannot be enabled, you may configure the internal MyWorkDrive viewer for office documents. The internal viewer does not have a seamless transition to editing, and places additional load on the MyWorkDrive server, so it is not the preferred option. When setting the internal MyWorkDrive viewer, it is advisable to also change the double click action to open as edit instead of view. Those changes are made in the Settings section of Server Administration.
Clustering
If you have clustering enabled with clustering of configuration files on an SMB path, all MyWorkDrive servers need to be able to reach the cluster config files via SMB.
If you have clustering of Sessions and Locks enabled via database, all MyWorkDrive servers need to be able to reach the database via the appropriate ports
Microsoft Settings (typically tcp port 1433)
PostgreSQL settings (typically tcp port 5432)
DMZ / LAN Ports and connections
MyWorkDrive has no requirements about placement regarding firewalls or use in a DMZ. It is up to you where you wish to place the MyWorkDrive server and how you want to make allowances for necessary connections to network resources.
For internal connections to LAN resources (AD, LDAP, SMB, DNS, etc,) MyWorkDrive uses traditional networking ports when connecting to LAN resources using Active Directory Identity (Entra ID Identity in Version 7 and later does not require LAN resources).
All external connections to the MyWorkDrive server inbound are on 443 (or the ports you choose when publishing with Proxies/Reverse Proxies) and 7844 outbound when using the Cloud Web Connector or cloudflare tunnels with Office Online or OneDrive/SharePoint/Azure storage.
LAN Ports Required
For MyWorkDrive using Active Directory Identity
According to Microsoft and other community discussions, these ports are required for servers to communicate with Active Directory and SMB resources.
| Application Protocol | Protocol | Port(s) |
|---|---|---|
| Active Directory Web Services (ADWS) | TCP | 9389 |
| Active Directory Management Gateway Service | TCP | 9389 |
| Global Catalog | TCP | 3268, 3269 |
| ICMP | No port number | |
| Lightweight Directory Access Protocol (LDAP) | TCP | 389 |
| Lightweight Directory Access Protocol (LDAP) | UDP | 389 |
| LDAP SSL | TCP | 636 |
| IPsec ISAKMP | UDP | 500 |
| NAT-T | UDP | 4500 |
| RPC | TCP | 135 |
| RPC randomly allocated high TCP ports | TCP | 49152 - 65535 |
| SMB | TCP | 445 |
| DNS | TCP | 53 |
| DNS | UDP | 53 |
| Kerberos | TCP | 88 |
| Kerberos | UDP | 88 |
| Kerberos Password V5 | TCP | 464 |
| Kerberos Password V5 | UDP | 464 |
High Number Dynamic Port Range
LDAP uses a high number dynamic range and these ports must be available for devices placed outside the firewall or in the DMZ to communicate with AD and Network Resources. You cannot block these ranges and have proper function with Active Directory.
Start port: 49152 End port: 65535
9389 ADWS
MyWorkDrive uses ADWS as part of the strategy to look up user group membership. Please ensure 9389 is available to the MyWorkDrive server.
Secure LDAP LDAPS 636 and 3269
MyWorkDrive doesn't directly connect to LDAP or AD. MyWorkDrive connects through the domain joined server MyWorkDrive is installed on. Connection to LDAPS is made between the host computer and domain, so if you wish to use LDAPS, ensure it is configured on the domain and the Windows Server MyWorkDrive is installed on is properly configured.
Both 636 and 3269 are required for proper operation.
Reference https://learn.microsoft.com/en-us/archive/technet-wiki/18254.active-directory-ldaps-636-and-msft-gc-ssl-3269-service https://learn.microsoft.com/en-us/troubleshoot/windows-server/identity/enable-ldap-over-ssl-3rd-certification-authority
Community Discussion https://learn.microsoft.com/en-us/archive/msdn-technet-forums/ff0fc815-69be-4239-8a03-27cfd444d04c https://learn.microsoft.com/en-us/archive/msdn-technet-forums/406bdeb4-3a52-422e-84c3-bf9444fc1751 https://petri.com/enable-secure-ldap-windows-server-2008-2012-dc/
LDAP with Channel Binding Alternative https://4sysops.com/archives/secure-domain-controllers-with-ldap-channel-binding-and-ldap-signing/
SSL/TLS Authenticity
It is imperative that any SSL/TLS certificates used in communications for MyWorkDrive
- For publishing access to MyWorkDrive for users
- For access to Identity Providers
- For access to Office Online Editing
- Between services such as Load balancers or Inbound/Outbound Proxies (particularly on workstations)
Are properly configured and are not altered in any way. Altered SSL/TLS will often result in rejected communication and failed connections to services.
This is particuarly common with Proxies, acting as a Man in the Middle, or when using SSL Offloading where a portion of the communication becomes unencrypted.
Licensing
Our licensing system uses Microsoft Traffic Manager and WebApps all in Azure. The IPs are managed by Microsoft for those services and subject to change.
Hostname
The hostnames that should be approved
- licensing.myworkdrive.net
- fe01.myworkdrive.net
- fe02.myworkdrive.net
IP Addresses
As a traffic manager solution, there are two Endpoints - Traffic Manager and the actual services. In both cases, there are IP Address ranges to maintain as published by Microsoft.
Traffic Manager
The traffic manager service uses different IPs based on region, so if you wish to maintain by IP, the Azure IP range for "AzureTrafficManager" is required.
The IP ranges can be downloaded in json from Microsoft Azure IP Range
Services
That is a traffic manager, it redirects to our service Endpoints, those would also need to be whitelisted.
Our Endpoints are Webapps hosted in Azure. Those also use an array of IPs that do occasionally change
At current 40.112.243.33, 104.40.63.98, 40.71.11.145
The complete IP Address ranges, as listed in the Azure IP Range would be "AppService.WestUS" and "AppService.EastUS".
Microsoft Sources
The MyWorkDrive installer streams dependencies from Microsoft such as .NET and Edge Webview2 as part of the installation process. The following Microsoft sources must be permitted for successful install of MyWorkDrive.
Specific Address to include:
*.dl.delivery.mp.microsoft.com TCP 443 msedge.api.cdp.microsoft.com TCP 443 go.microsoft.com TCP 443
builds.dotnet.microsoft.com TCP 443 dotnet.microsoft.com TCP 443 aka.ms TCP 443 download.visualstudio.microsoft.com TCP 443 # legacy, safe to include
Details
Domains to allow for Edge Webview2
Domains to Allow (HTTPS/443) These are the primary domains involved in a WebView2 bootstrapper stream install: Core download delivery (CDN): To simplify the allowlist for download locations, a wildcard can be used: *.dl.delivery.mp.microsoft.com More specifically, the msedge delivery nodes are:
msedge.sf.dl.delivery.mp.microsoft.com msedge.sf.tlu.dl.delivery.mp.microsoft.com msedge.b.dl.delivery.mp.microsoft.com msedge.b.tlu.dl.delivery.mp.microsoft.com msedge.f.dl.delivery.mp.microsoft.com msedge.f.tlu.dl.delivery.mp.microsoft.com msedge.sb.dl.delivery.mp.microsoft.com msedge.sb.tlu.dl.delivery.mp.microsoft.com
Update/metadata services:
msedge.api.cdp.microsoft.com go.microsoft.com
Bootstrapper initial download link:
go.microsoft.com (resolves the fwlink redirect for the bootstrapper itself) msedge.sf.dl.delivery.mp.microsoft.com (where the actual runtime payload comes from)
Domains to Allow for .NET Downloads Primary CDN (current):
builds.dotnet.microsoft.com — this is where the install scripts actually pull binaries from Microsoft dotnet.microsoft.com — landing page and redirect source
Redirect/short-link service:
aka.ms — short links use aka.ms which produces 301 redirects that forward to the CDN, so your firewall needs to allow the redirect chain, not just the final destination
Legacy domains (still functional but being wound down):
download.visualstudio.microsoft.com — Microsoft plans to stop using this for new content, but the CDN will continue to function for existing content dotnetcli.azureedge.net — old domain, avoid relying on it
Metadata/release index:
dotnet.microsoft.com (also serves release metadata JSON)
The Recent CDN Migration (Important) Microsoft migrated .NET binaries and installers to a new domain — builds.dotnet.microsoft.com — backed by a new CDN. This happened because the previous CDN domains ending in .azureedge.net were hosted by edg.io, which ceased operations due to bankruptcy. If you have any old firewall rules referencing dotnetcli.azureedge.net, those need to be updated.
References
- Microsoft Learn – WebView2 deployment and distribution
- Microsoft Learn – WebView2 firewall and proxy allowlisting
- Microsoft – .NET install scripts and CDN migration to builds.dotnet.microsoft.com
- Microsoft – .NET download domains and aka.ms redirect behavior
- Microsoft – Visual Studio / .NET CDN legacy domain transition
