Contents
Always On VPN Security & Support Concerns
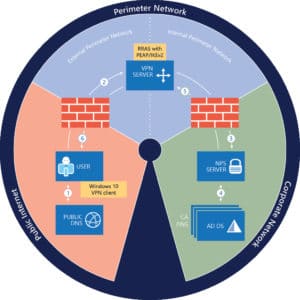
Starting with Windows Server 2016′ “Always On VPN” provides new options for remote access to internal network resources. With Windows 10 Virtual Private Networking (VPN), you can create connections so that remote computers and devices are always connected to your organization network when they are turned on with the an Internet connection.
Considerations when deploying Always On VPN
We looked at the requirements for Windows Always On VPN’s to determine if they are more secure or easier to administer and use than Direct Access or 3rd Party VPN’s. Here are potential items that may lead to additional support costs and security concerns that enterprises will want to be aware of.
- AO VPN cannot be managed natively using Active Directory and group policy. It must be configured and managed using Microsoft System Center Configuration Manager (SCCM), Microsoft Intune, or PowerShell.
- AO VPN works only with Windows 10. It is not supported for Windows 7 or other operating systems.
- While AO VPN does add extensive filtering options, no additional blocking technologies exist to prevent viruses or malware, such as crypto locker, from encrypting files.
- A Public Key Infrastructure (PKI) is required along with Active Directory Certificate Services to authenticate clients.
- Like Direct Access, AO VPN requires two network adapters with one directly connecting to the external perimeter network.
- Remote Client Computers must be joined to the active directory domain.
- The IT Department will need to maintain an additional fleet of corporate laptops with VPN pre-configured for each potential remote user eliminating the BYOD option.
- Using an AO VPN violates the principal of Zero Trust least privileged access as noted by ZScaler detailed in our article here.
Browser Based VPN Alternatives
Tech Target encourages companies to consider Web Based VPN Software Alternatives – “Browser-based remote access services offer both cost and ease-of-use advantages. Web browsers are already present on nearly every computing device, public or private, large or small. Web-based solutions use this browser and dynamically downloaded code to avoid installing and configuring VPN client software on the worker’s device. This approach facilitates remote access from just about anywhere and can significantly reduce per-user VPN administration costs. Savings are even greater for companies that eliminate corporate laptops by leveraging existing desktops for Web-based remote access.”
MyWorkDrive VPN Alternative
MyWorkDrive’s https clients and browser based file access software helps companies reduce their VPN support costs while reducing their security exposure risks as an alternative to VPN. Users simply open a browser to access their work files using their existing Windows Active Directory credentials from any device. Once logged in, they can access company shares and home drives, and edit/view documents online. For security, all MyWorkDrive clients also have DUO Two Factor, Support SAML SSO, Device Approval and Data Leak Prevention. Even if only half of a company’s employees are directed to use MyWorkDrive’s Browser Based File Access client, they can achieve annual savings of up to 50% while improving security when compared to other VPN alternatives.
